This guide describes the Assertion Signing Key specification, how to generate a JSON Web Token (JWT) from the signing key, and how to issue a channel access token v2.1 using the generated JWT.
- Generate Jwt Token With Private Key
- Generate Jwt Token With Keys
- Generate Jwt Token With Public Key
- Generate Jwt Token With Private Key Python
- Generate Jwt Token With Secret Key
- Generate Jwt Token With Private Key C#
# Diagram for issuing a channel access token v2.1
Create and Sign a JSON Web Token (JWT) with C# and.Net.Net comes with handy tools to deal with JWT Tokens. Just add the following Microsoft packages as dependencies of your.Net project: Microsoft.IdentityModel.Tokens; System.IdentityModel.Tokens.Jwt. JWT tokens are signed using a secret or key selected by the manager of the access profile. JWT tokens are used by identity providers (for example Okta, OneLogin, Auth0) that authenticate users and provide verified access to business applications.
ACCESSTOKENSECRET is a secret key you use to generate JWT, In the example we are saving it in constant but for security, you should use an environment variable to pass this key. Below code will generate a 32 bytes secret or you can use any random secret code. Create and Sign a JSON Web Token (JWT) with C# and.Net.Net comes with handy tools to deal with JWT Tokens. Just add the following Microsoft packages as dependencies of your.Net project: Microsoft.IdentityModel.Tokens; System.IdentityModel.Tokens.Jwt.
This diagram shows these three steps:
- Create an Assertion Signing Key (Step 1 in the diagram)
- Generate a JWT (Step 6 in the diagram)
- Issue channel access tokens v2.1 (Step 7 in the diagram)
The authentication method for issuing a channel access token v2.1 is in accordance with Using JWTs as Authorization Grants(RFC 7523)(opens new window). This is the Assertion Framework of OAuth Assertion Framework(RFC 7521)(opens new window) using JSON Web Token(RFC 7519)(opens new window).
# Create an Assertion Signing Key
Issuing an Assertion Signing Key is done in the these two steps:
# 1. Generate a key pair for the Assertion Signing Key
In order to generate a JWT, you must first generate a key pair (private key, public key) for the Assertion Signing Key.
# Assertion Signing Key specification
You can use a JSON Web Key(RFC7517)(opens new window) that meets these criteria as an Assertion Signing Key for JWT.
- Must be an RSA public key (
RSAis configured in thektyproperty). - RSA key length is 2048bit.
- RS256 (RSASSA-PKCS1-v1_5 with SHA256) is used in the signing algorithm (
RS256is configured in thealgproperty). - Must state that the public key will be used for signing (appropriate value configured in either
useorkey_ops).
Therefore, the public key of the Assertion Signing Key must contain these fields:
| Property | Description |
|---|---|
kty | Cryptographic algorithm family used in key. Specify RSA. |
alg | Algorithm used in key. Specify RS256. |
use | Use of key. Specify sig.*1 |
key_ops | Operation where key is expected to be used. Specify ['verify']. Exclude elements other than verify. *1 |
e | Absolute value for restoring public key. |
n | Cryptographic index for restoring public key. |
*1 Valid if one of either use or key_ops is specified.
kid is issued when a public key is registered in the LINE Developers Console. If the public key contains kid, an error will occur. Make sure the public key you are about to register doesn't contain kid.
The key pair for the Assertion Signing Key can be generated by the developer's own program based on the published specification, but it can be generated more easily by using a library that meets the specification.
Here are two examples of the steps to generate an Assertion Signing Key:
# Generate using Go language command line tools
You can generate a key pair using jwx command line tool(opens new window), which is a part of jwx(opens new window), an open source Go language library used for implementing JWT. Use these steps to issue an Assertion Signing Key.
# 1. Install jwx command line tool
To install the jwx command line tool, a Go language development environment is required beforehand. You can download the development environment from the Go language official site(opens new window).
Execute this command from the path where you installed Go to install the jwx command line tool.
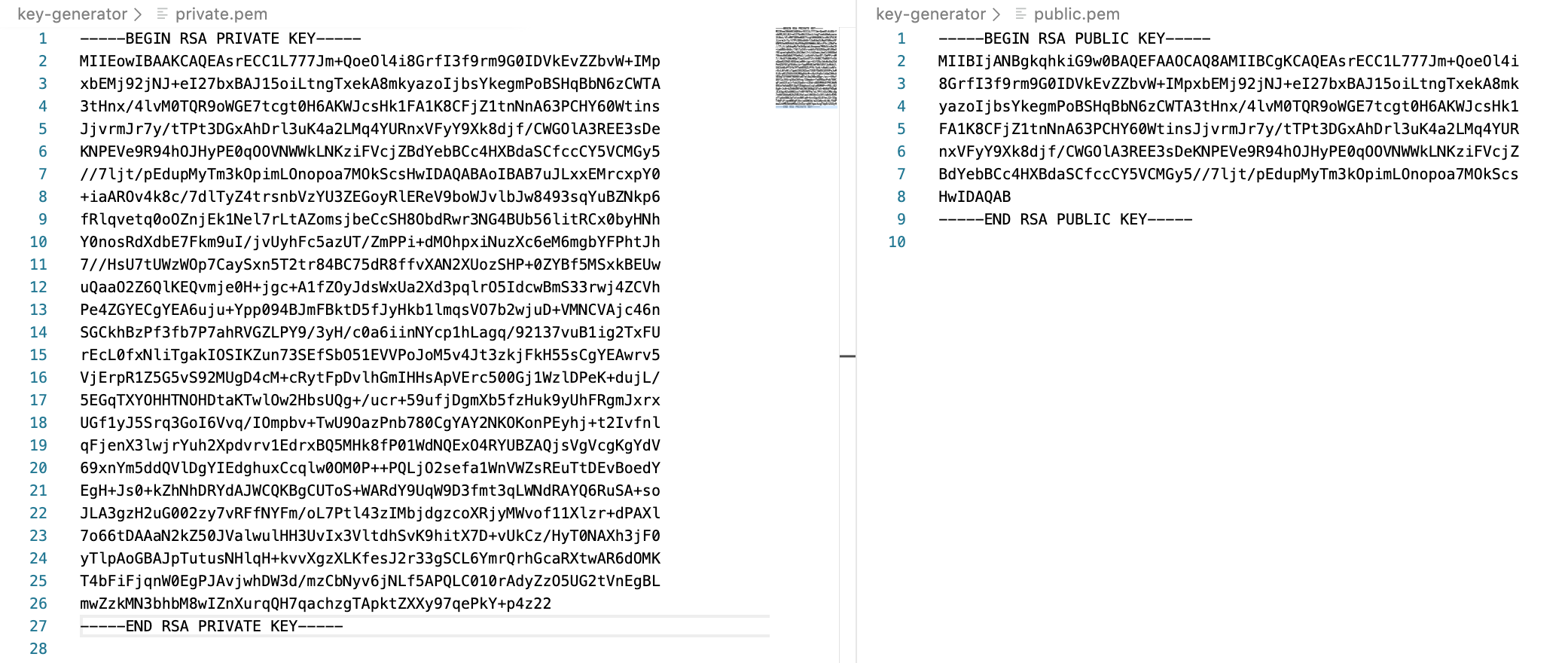
# 2. Generate private key and public key
Use the same path to execute this command and generate a private key.
Generate Jwt Token With Private Key
Use this command to generate a public key based on the private key.
If you succeed, a private key (private.key) and public key (public.key) will be generated as below.
private.key example:
public.key example:
# Generate using browser
If your browser supports Web Crypto API(opens new window), you can use the SubtleCrypto.generateKey()(opens new window) method to generate a private key and public key.
Enter this code on your web browser's developer console and execute.
If you succeed, the following private key (private.key) and public key (public.key) are generated.
private.key example:
public.key example:
# 2. Register public key and get kid
Select your channel from the channel settings on the LINE Developers Console and access the Basic settings tab. Next, click the Register public key button next to Assertion Signing Key and enter the public key generated in step 1. Click the Register button.
kid will be displayed if you succeed in registering your public key.
# Generate a JWT
You can use any JWT library(opens new window) or write your own code from scratch to generate a JWT from your Assertion Signing Key.
This is an example created using a JavaScript library introduced in JWT(opens new window). To use this code, you'll need to install these items:
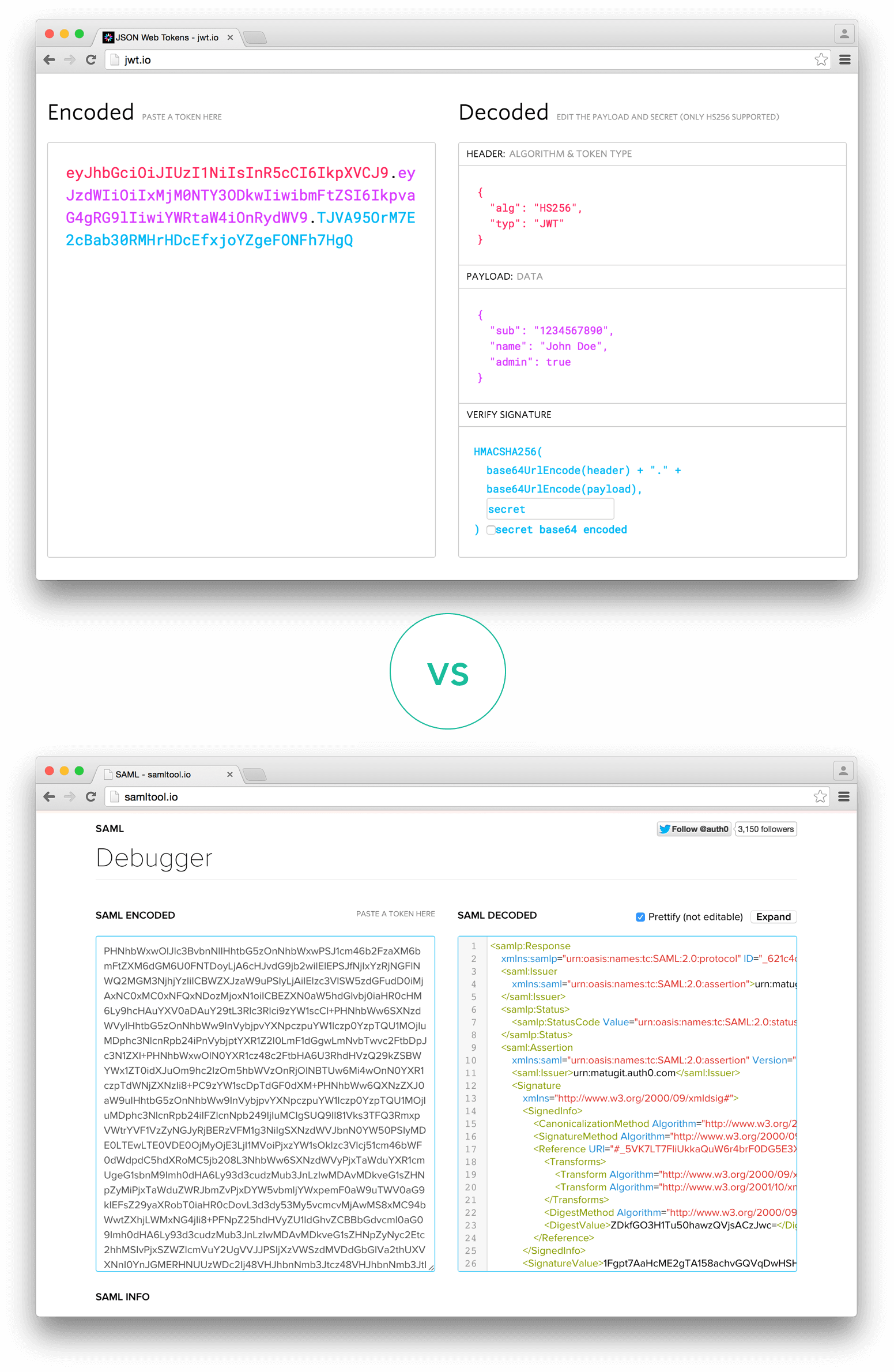
The JWT is a string made up of a header, payload, and signature; all are required fields.
Generate Jwt Token With Keys
Header
| Property | Description |
|---|---|
alg | Fixed property: 'RS256' |
typ | Fixed property: 'JWT' |
kid | Use the kid property obtained in Create an Assertion Signing Key. |

This is an example of a decoded header value.
Payload
| Property | Type | Description |
|---|---|---|
iss | String | Channel ID. Found on the LINE Developers Console. Must be equal to sub. |
sub | String | Channel ID. Found on the LINE Developers Console. Must be equal to iss. |
aud | String | https://api.line.me/ |
exp | Number | The expiration time of the JWT. Set this value in UNIX timestamp. The max lifetime of a JWT Assertion is 30 minutes. |
token_exp | Number | Required when requesting a channel access token. This represents a valid expiration time for the channel access token in seconds. The max lifetime of a channel access token is 30 days. |
This is an example of a decoded payload value.
Signature
Generate Jwt Token With Public Key
You can generate a JWT by signing the header and payload as shown above with your private key of your Assertion Signing Key.
This is an example of the code used to generate a JWT signed with a private key using node-jose. To create your own JWT with this code, change the privateKey to the value of the private key of your Assertion Signing Key and change the values of header and payload, respectively, and run it. See node-jose(opens new window) for more information on how to use node-jose. Be sure to sign with your private key to prove that the content has not been tampered with.
Example code using node-jose
Sign the base64url-encoded header, base64url-encoded claim set, and a secret key (such as an rsa_private.pem file) using the algorithm you defined in the header. The signature is then base64url-encoded, and the result is the JWT.
Example encoded JWT
# Issue channel access tokens v2.1
You can issue a channel access token v2.1 with the JWT assertion, generated by the procedure in Generate a JWT, specified.
- The response when issuing a channel access token v2.1 includes a channel access token and a unique key ID (
key_id) pair. To manage channel access tokens correctly, be sure to store the channel access token and key ID pair at the time of issuing. - The key ID is an identifier added to the Messaging API on June 22, 2020. If your app is using a channel access token v2.1 that doesn't have a key ID, we encourage you to re-issue a channel access token v2.1 and store the token and key ID pair. Change your app to always use the new token if the channel access token is re-issued.
Generate Jwt Token With Private Key Python
- To issue a channel access token, specify the generated JWT and execute the Issue channel access token v2.1 endpoint.
- Channel access token and key ID are returned from the LINE Platform.
- Store the channel access token and key ID pair in a database or other location.
# Revoke channel access token v2.1
You can revoke a channel access token v2.1 with a valid channel access token specified.
Generate Jwt Token With Secret Key
Even if specifying an invalid channel access token and executing the Revoke channel access token v2.1 endpoint, no error occurs. To get key IDs paired to the current valid channel access tokens, execute the Get all valid channel access token key IDs v2.1 endpoint.To identify the valid access token, match the obtained key ID to its respective channel access token.
Generate Jwt Token With Private Key C#
- Re-generate a JWT from the stored assertion signing key.
- Execute the Get all valid channel access token key IDs v2.1 endpoint with the JWT specified.
- The valid channel access token and key ID are returned from the LINE Platform.
- Explore the database that stores the channel access token and key ID pair.
- Search for the channel access token and key ID pair that match the obtained key ID.
- Get the valid channel access token.
- Specify the valid channel access token and execute the Revoke channel access token v2.1 endpoint.
- The channel access token is revoked from the LINE Platform.